A Scenario-Based eLearning Solution for Contact Center Agents
Overview
In this interactive, scenario-based eLearning course, contact center agents learn to recognize and respond to common social engineering tactics that fraudsters use to gain access to sensitive customer and company data. Through real-world scenarios, agents practice using verification procedures and gain confidence in handling these situations while maintaining top-quality customer service.
- Audience: new and experienced contact center agents
- Responsibilities: Action mapping, storyboarding, visual and graphic design, eLearning development, instructional design
- Tools used: Articulate Storyline 360, Canva, Adobe, Google Docs, MindMeister
The Problem
t client, a major sportswear and equipment retailer, was facing increased fraud attempts through social engineering in their contact centers. By working with subject matter experts, we identified that agents were vulnerable to manipulation and often struggled to balance data security with customer satisfaction. This highlighted the need for a dedicated training focused on social engineering prevention and data protection.
The Solution
I proposed a scenario-based eLearning approach, allowing agents to engage with simulated real-life situations where data breaches could occur due to social engineering tactics. This format helps build both the knowledge and confidence agents need to effectively apply verification processes, enhancing the quality of customer interactions and reducing the risk of data breaches.
My Process
Instructional Design (ADDIE Model)
Following the ADDIE model, I analyzed the content gaps in previous agent training programs, particularly around data protection and decision-making. It became clear that we also needed to refresh agents on current verification procedures, making this training a timely addition.
Collaboration with SMEs
Through detailed discussions with SMEs, we identified common social engineering challenges agents face. Together, we documented these scenarios, focusing on moments where agents must decide how to proceed while safeguarding sensitive information.
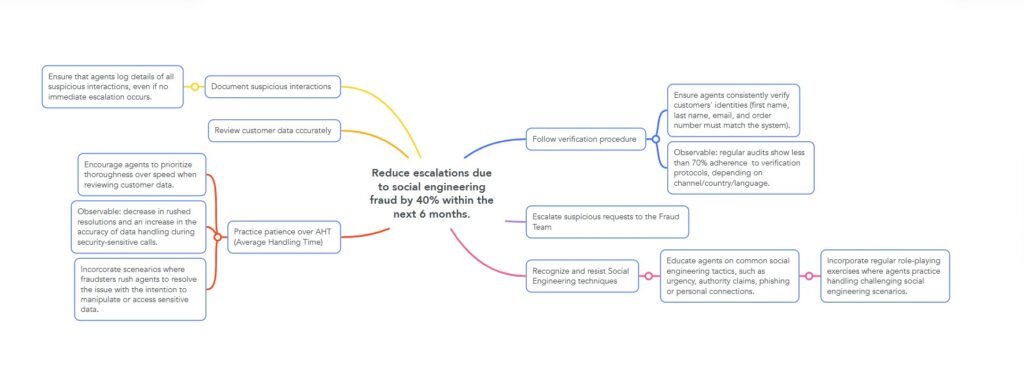
Action Mapping
Our goal was to reduce escalations due to social engineering fraud by 40% by the end of Q4 following the course implementation. Using action mapping, we pinpointed high-priority actions to ensure agents effectively apply verification steps under pressure.
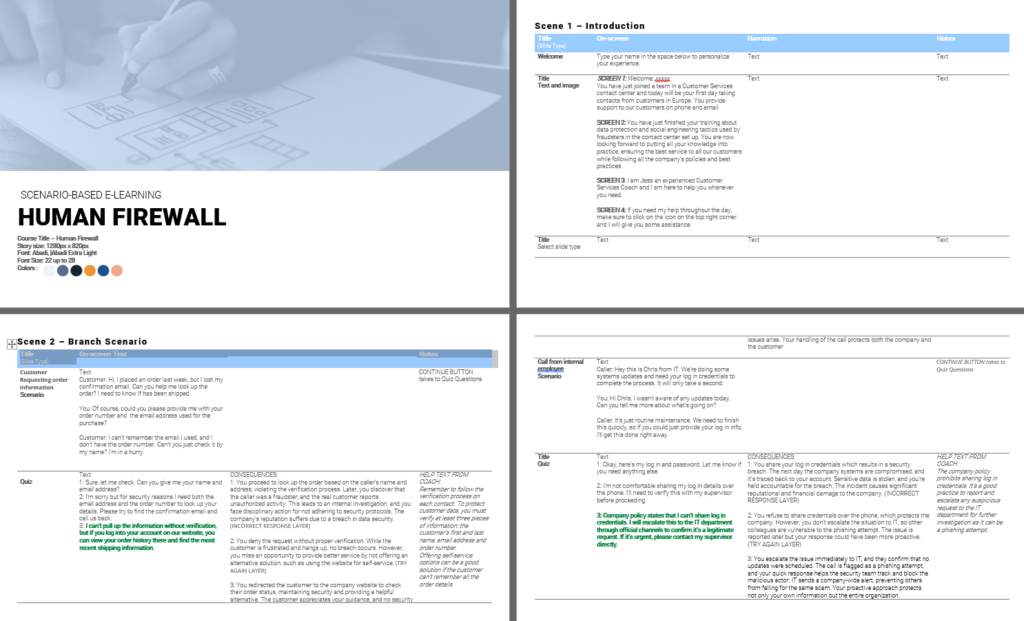
Storyboard and Mentorship Design
To visualize the course, I created a text-based storyboard that outlined each scenario. I aimed to immerse learners in relatable situations, using a light, conversational tone that encourages learning through feedback. Additionally, I introduced a mentor character, “Olivia,” who offers context and support to agents throughout the training. This approach helps agents feel guided while maintaining autonomy in decision-making.
Visual Design and Mockups
Starting with a mood board, I experimented with color schemes and fonts, ultimately creating a style guide that was inviting and calming. This design foundation was crucial in making agents feel comfortable as they explored challenging topics.




Full Development and Prototype Testing
The prototype phase allowed me to collect valuable feedback and refine the course layout before moving to full development. Using Articulate Storyline 360, I designed interactive scenarios with triggers, states, and animations to keep agents engaged. I prioritized making each scenario intuitive and impactful to maximize retention.
Results and Reflections
Once the project was completed, I shared it with peers and received positive feedback, with many learners expressing they felt better equipped to handle potential fraud situations. This experience deepened my passion for instructional design and has reinforced my commitment to creating impactful, learner-centered solutions.